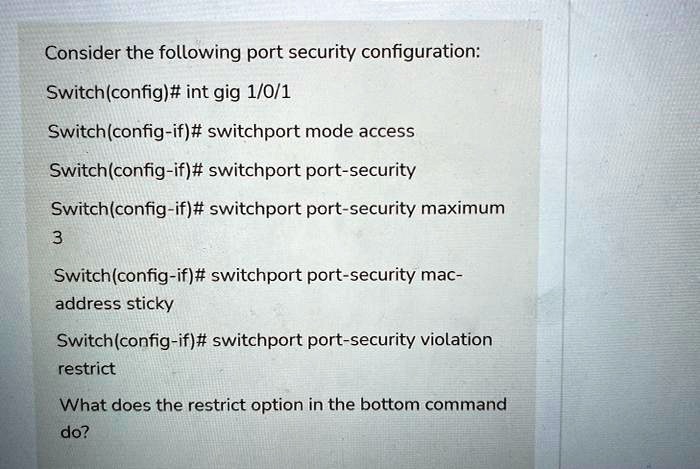
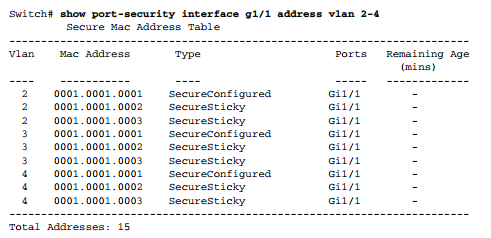
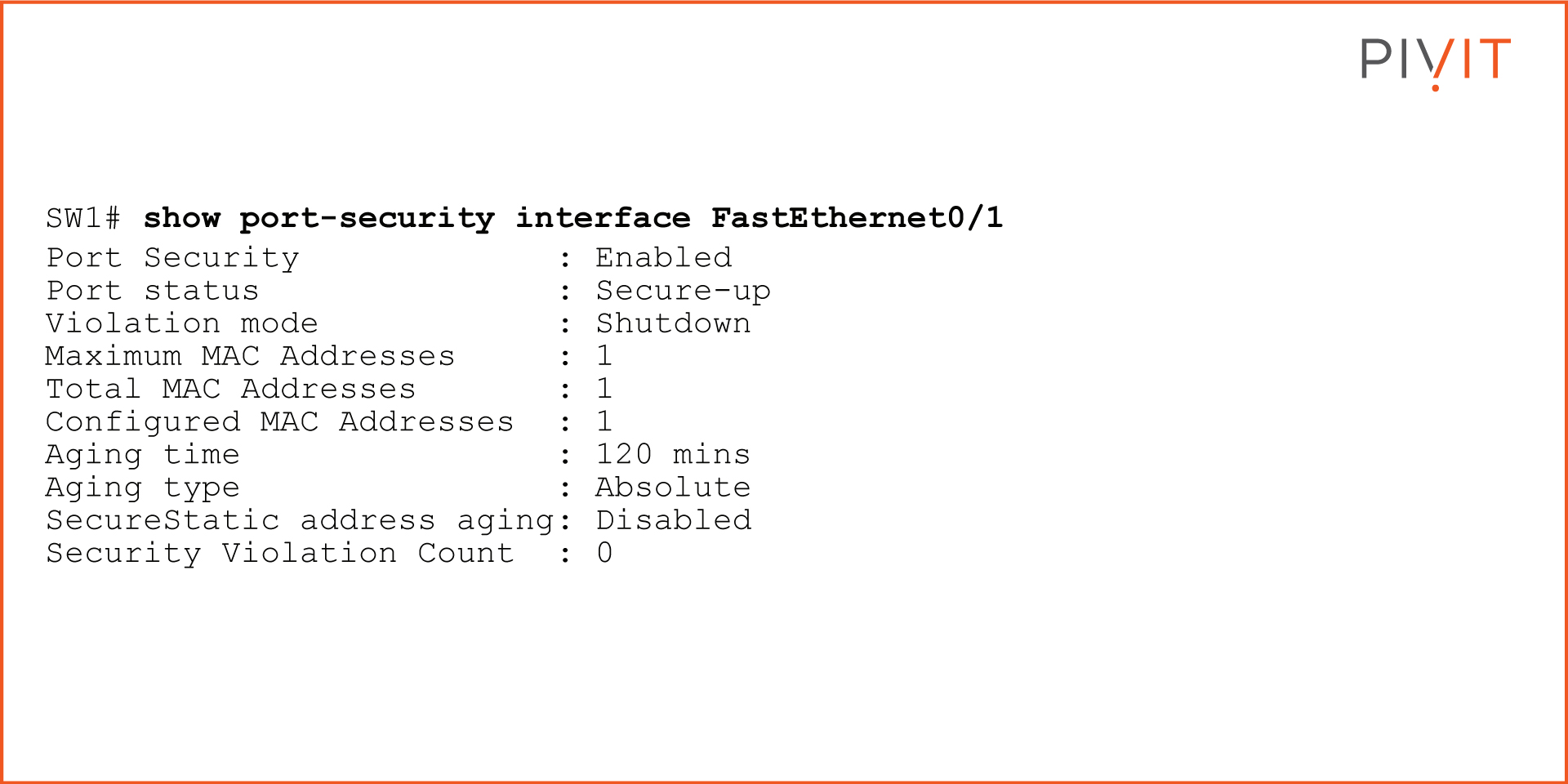
SOLVED: Consider the following port security configuration: Switch(config)# interface gig 1/0/1 Switch(config-if)# switchport mode access Switch(config-if)# switchport port-security Switch(config-if)# switchport port-security maximum 3 Switch(config-if ...

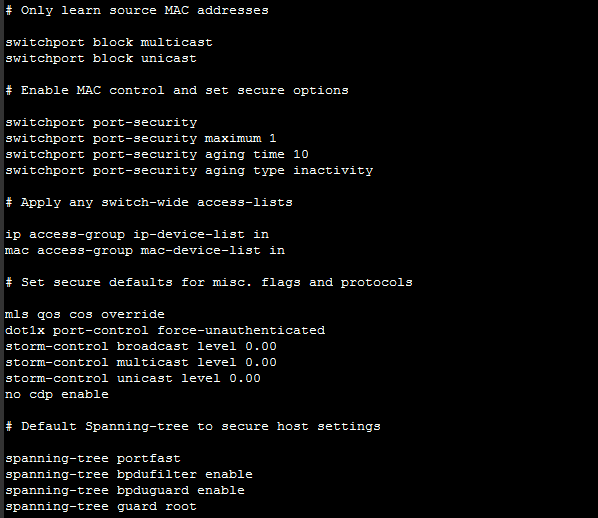
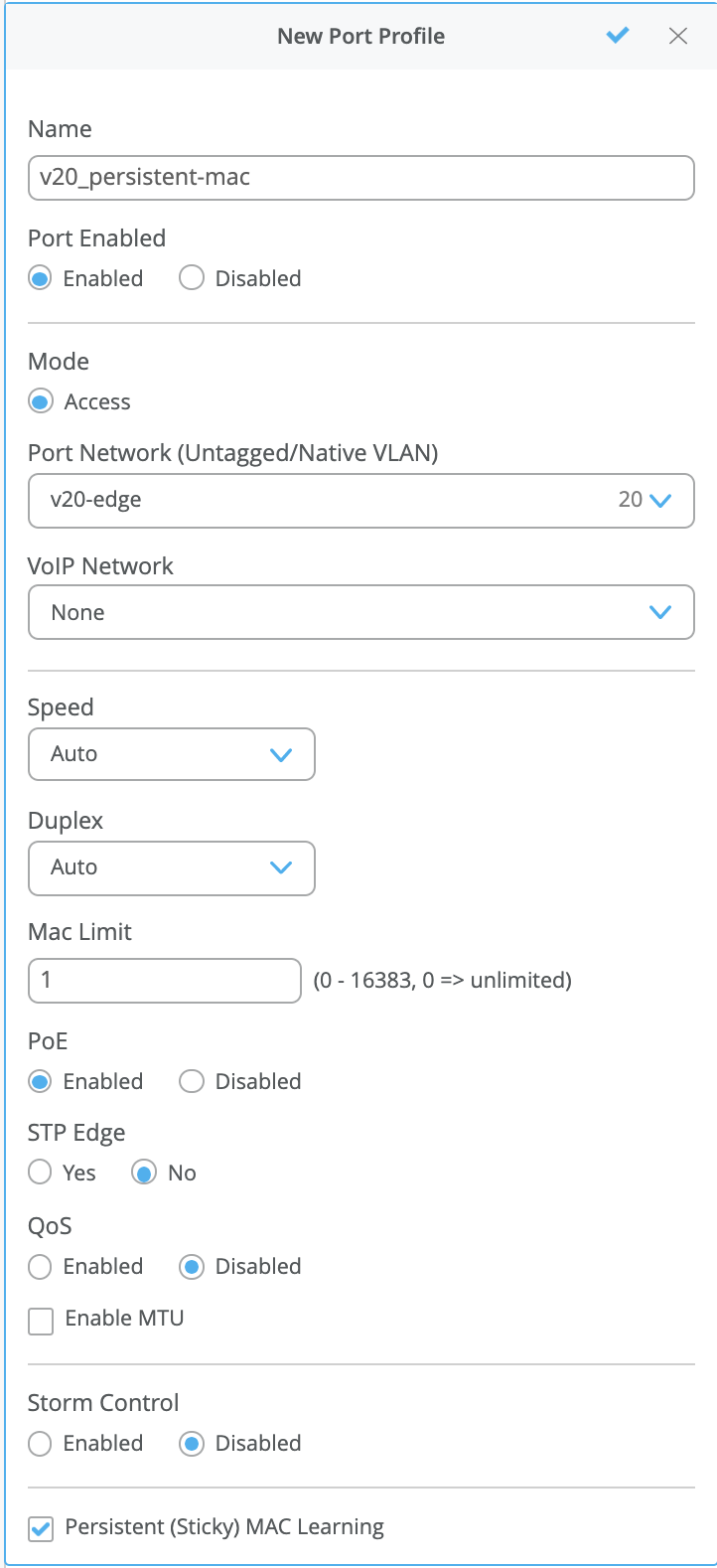
MAC layer control - Sticky MAC and MAC Learning-limit | FortiGate / FortiOS 6.2.15 | Fortinet Document Library

Switch Port Security Access Control List (ACL) Configuration on Cisco... | Download Scientific Diagram

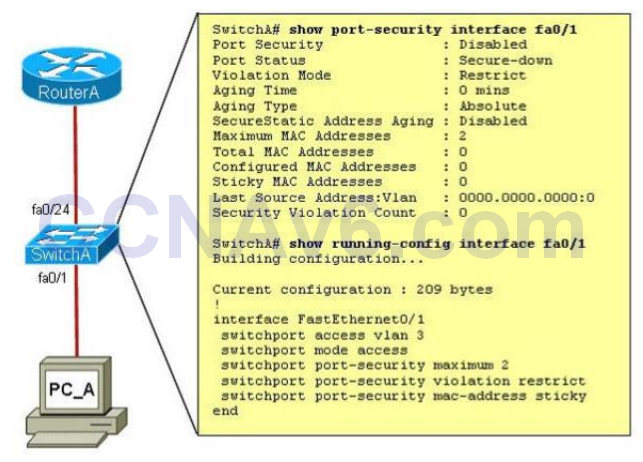
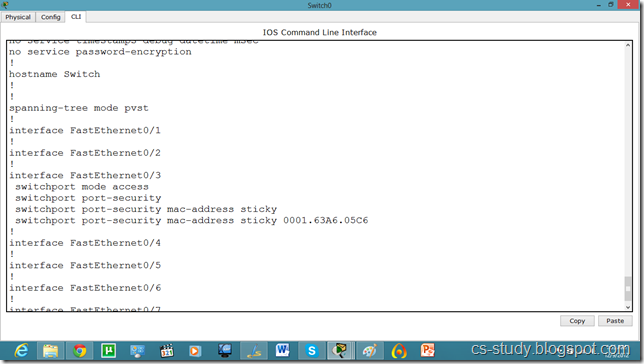
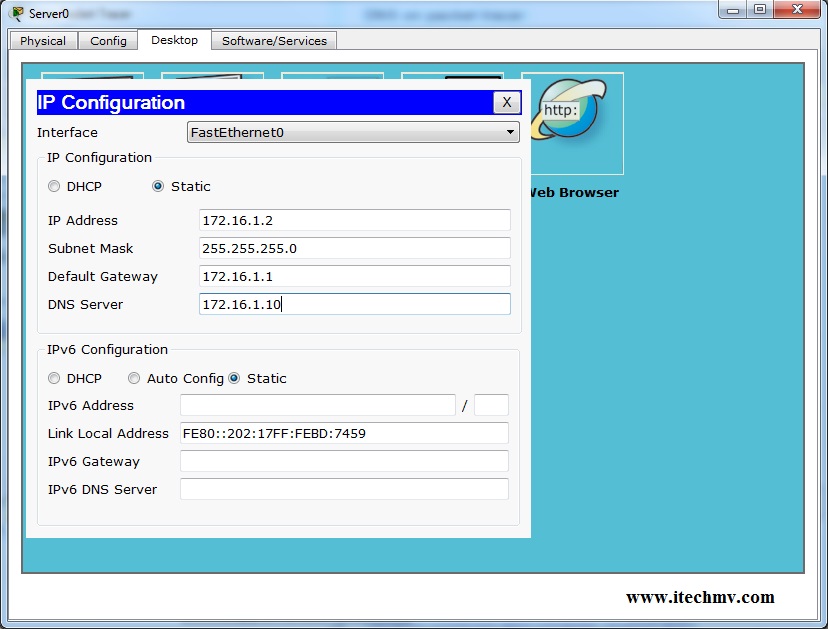
Internetworks: What is cisco port security? How to secure switches ports? | What are the violations of port security? | How to configure?







![SOLVED] how to allow one mac address in multiple ports in cisco switch port-security? SOLVED] how to allow one mac address in multiple ports in cisco switch port-security?](https://content.spiceworksstatic.com/service.community/p/post_images/0000025710/53b043d5/attached_image/Untitled.png)